Mini Program vs Micro Frontend: Architectural Decisions for Modern Application Development
Mini programs and micro frontends represent two distinct architectural approaches for building modular, scalable applications, each with different technical characteristics, implementation requirements, and organizational implications. Understanding these differences is essential for development teams making architectural decisions that balance technical requirements, team structure, and business objectives in modern application environments.
Technical Architecture and Implementation Patterns
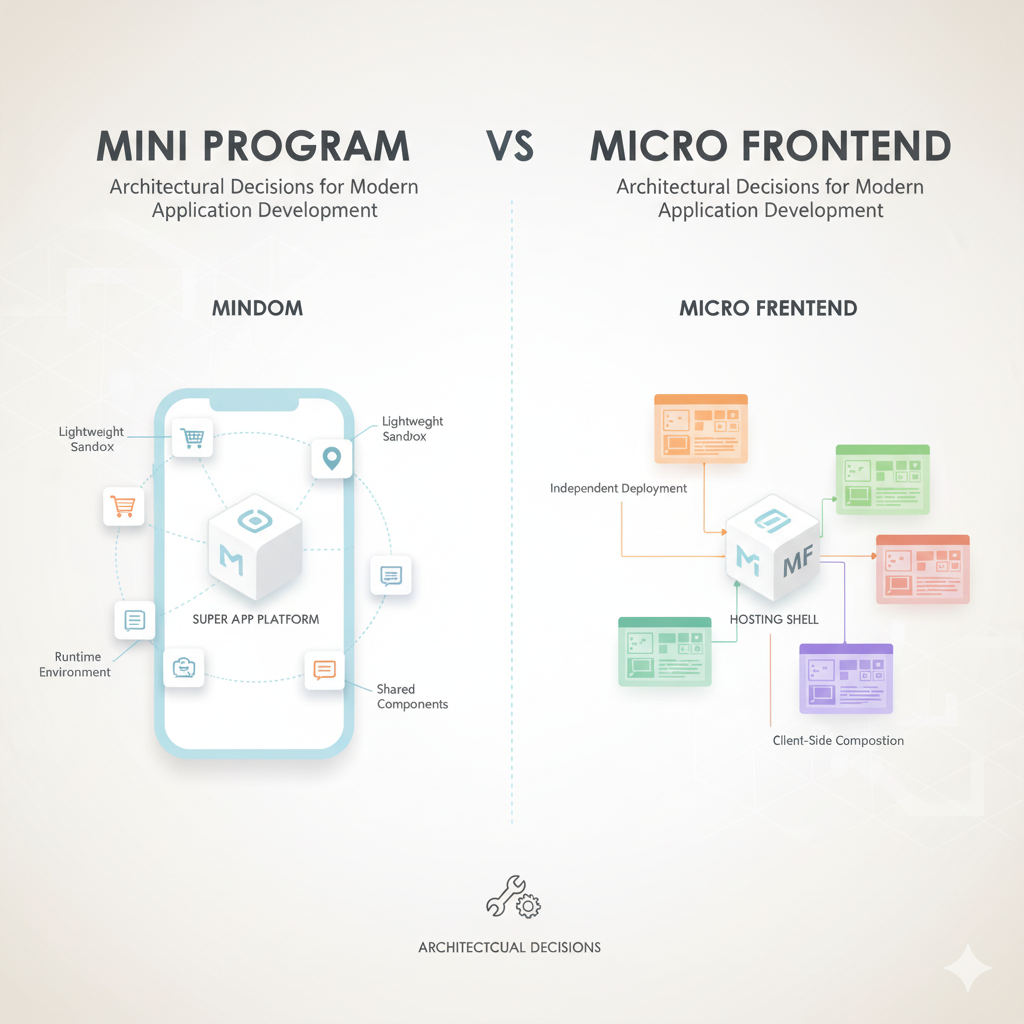
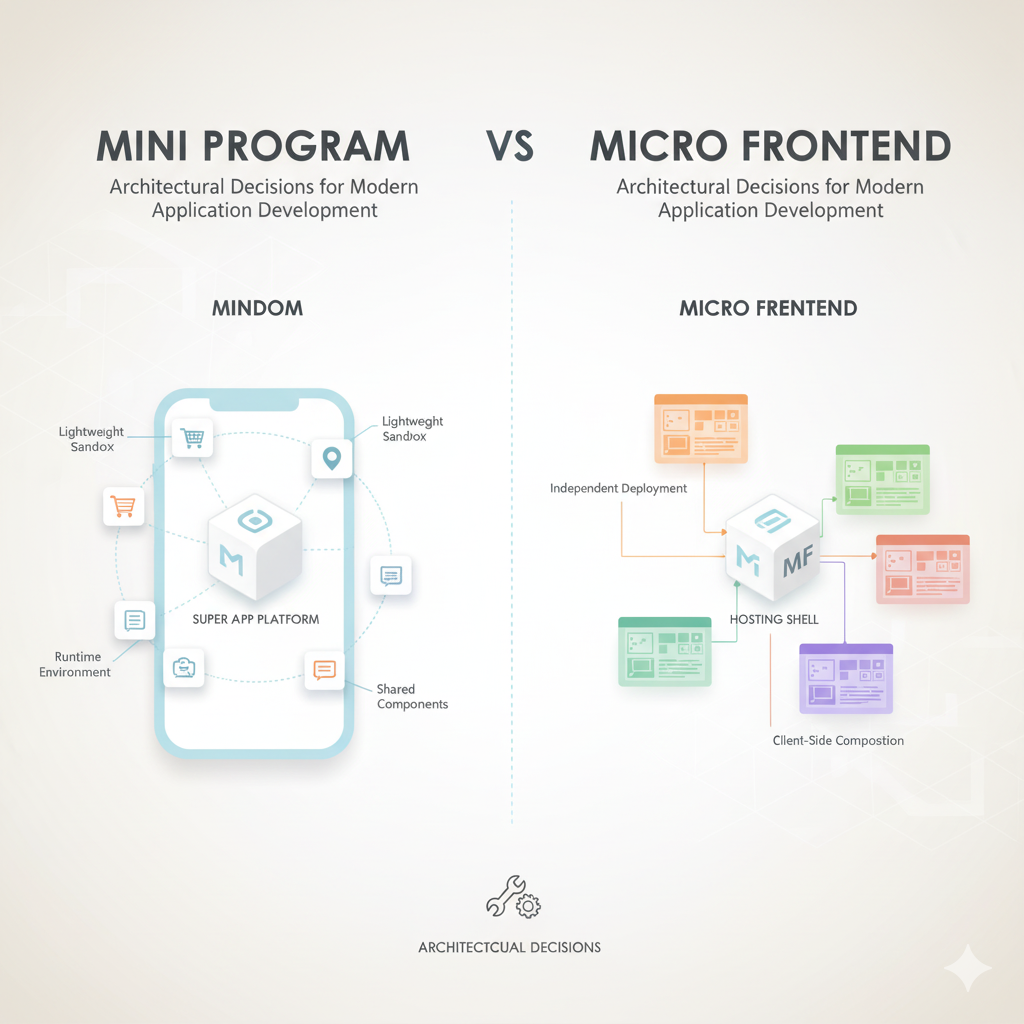
Mini programs operate as containerized applications within host platforms like WeChat, Alipay, or Baidu, utilizing platform-specific APIs and runtime environments. They typically employ lightweight frameworks (often JavaScript-based) that execute within sandboxed environments, with strict size limitations (usually 2-10MB) and predefined lifecycle management. The container provides standardized access to device capabilities (camera, location, storage) and platform services (payments, user identity, social sharing), creating consistent development patterns across different mini programs within the same ecosystem.
Micro frontends adopt a different approach, decomposing monolithic frontend applications into independently deployable components that can be developed, tested, and released by autonomous teams. Implementation patterns vary significantly: some use iframe isolation, others employ Web Components with shadow DOM encapsulation, while more sophisticated implementations use module federation or runtime integration techniques. Unlike mini programs, micro frontends don't inherit standardized container services—each component must implement or integrate necessary capabilities independently or through shared libraries.
The deployment and distribution models differ fundamentally. Mini programs deploy through centralized platform app stores with standardized review processes, version management, and update distribution controlled by platform operators. Micro frontends deploy through conventional web infrastructure—CDNs, versioned URLs, or sophisticated feature flag systems—giving development teams more control over release timing and user exposure but requiring more complex deployment orchestration.
Performance and User Experience Considerations
Mini programs offer predictable performance characteristics within their container environments. Startup times typically range from 1-3 seconds for initial loads and 200-500ms for subsequent launches from cache, with memory usage limited by container constraints. The standardized runtime allows platform operators to optimize performance across the entire ecosystem—for example, preloading common frameworks or implementing aggressive caching strategies that benefit all mini programs uniformly. However, this standardization comes at the cost of flexibility; developers cannot implement custom performance optimizations that deviate from platform guidelines.
Micro frontend performance varies dramatically based on implementation choices. Well-architected systems using code splitting, lazy loading, and shared dependency management can achieve sub-second component loads with efficient bundle sizes. Poor implementations suffer from duplicated dependencies, excessive bundle sizes, and coordination overhead that degrades performance. The performance optimization burden shifts from platform operators to development teams, requiring sophisticated monitoring, analysis, and optimization efforts that many organizations underestimate during initial architecture planning.
User experience consistency presents another key distinction. Mini programs inherit platform design systems and interaction patterns, ensuring consistent navigation, gestures, and visual design across different applications within the same ecosystem. This reduces user learning curves but limits design differentiation. Micro frontends can maintain consistency through shared design systems and component libraries, but achieving true consistency requires disciplined governance and technical enforcement that many organizations struggle to implement effectively across autonomous teams.
Organizational and Development Workflow Implications
Mini program development typically follows platform-prescribed workflows with integrated development tools, standardized testing environments, and predefined deployment pipelines. This reduces infrastructure overhead and accelerates initial development but locks teams into platform-specific toolchains and processes. Team structure tends toward vertical integration within the mini program boundary, with developers responsible for frontend, backend integration, and platform-specific adaptations within cohesive units.
Micro frontend architectures enable true team autonomy, allowing independent development, testing, and deployment cycles for different application components. This supports scaling development organizations and parallelizing work on complex applications. However, this autonomy requires sophisticated coordination mechanisms: shared contracts for component interfaces, version compatibility management, cross-team dependency tracking, and coordinated release planning. The organizational overhead of these coordination mechanisms often represents 20-30% of total development effort in mature micro frontend implementations.
The skill requirements differ significantly. Mini program development demands expertise in specific platform ecosystems—understanding proprietary APIs, compliance requirements, and distribution mechanisms. Micro frontend development requires broader architectural knowledge: build tool configuration, dependency management, performance optimization, and cross-team coordination patterns. Organizations transitioning between approaches often underestimate the retraining requirements and architectural learning curves involved.
Security and Maintenance Trade-offs
Security models represent another critical distinction. Mini programs operate within platform-enforced sandboxes with predefined security boundaries, standardized permission models, and platform-managed updates for security vulnerabilities in shared runtime components. This reduces the security burden on individual development teams but creates dependency on platform operators for timely security patches and vulnerability responses. The closed ecosystems also limit integration possibilities with external security tools and monitoring systems.
Micro frontend security responsibility resides entirely with development organizations. Each component must implement appropriate security measures, vulnerability scanning, dependency management, and update processes. While this provides flexibility to implement organization-specific security requirements and integrate with preferred security tooling, it also requires dedicated security expertise and ongoing vigilance that many development teams lack. The distributed nature of micro frontends can also complicate security auditing and compliance documentation.
Maintenance complexity follows different patterns. Mini program maintenance involves managing dependencies on evolving platform APIs and ensuring compatibility with container updates that may introduce breaking changes. Platform operators typically provide migration paths and compatibility timelines, but teams must allocate resources specifically for platform adaptation work. Micro frontend maintenance involves managing dependency graphs across autonomous teams, version compatibility between independently evolving components, and coordinating updates to shared infrastructure—a coordination challenge that increases non-linearly with team count and component complexity.
Getting Started with Lightweight Integration Approaches
Organizations evaluating these architectural options should begin with clear assessment of primary requirements: if rapid deployment within established ecosystems with predictable performance and reduced infrastructure overhead is paramount, mini programs offer compelling advantages. If organizational scalability, technology flexibility, and integration with existing development toolchains are higher priorities, micro frontends warrant serious consideration regardless of their implementation complexity.
Hybrid approaches are increasingly viable. Lightweight container technologies enable mini-program-like experiences within native applications while maintaining development flexibility. These approaches use small SDKs (typically 2-5MB) that provide standardized runtime environments, device access abstractions, and update mechanisms without locking developers into specific platform ecosystems. This model offers middle-ground benefits: consistent user experiences across deployment targets, simplified update distribution, and reduced platform dependency while maintaining technology flexibility.
The 3MB SDK approach provides sandbox isolation similar to Docker containers but for application-level components, enabling secure execution of third-party code within existing applications. This architecture supports both mini-program-style ecosystems and micro frontend flexibility, creating adaptable foundations for evolving application requirements. Explore this open-source implementation that bridges architectural approaches while maintaining security and performance characteristics. GitHub