Mini-Program Containers Explained: Technical Architecture and Enterprise Applications
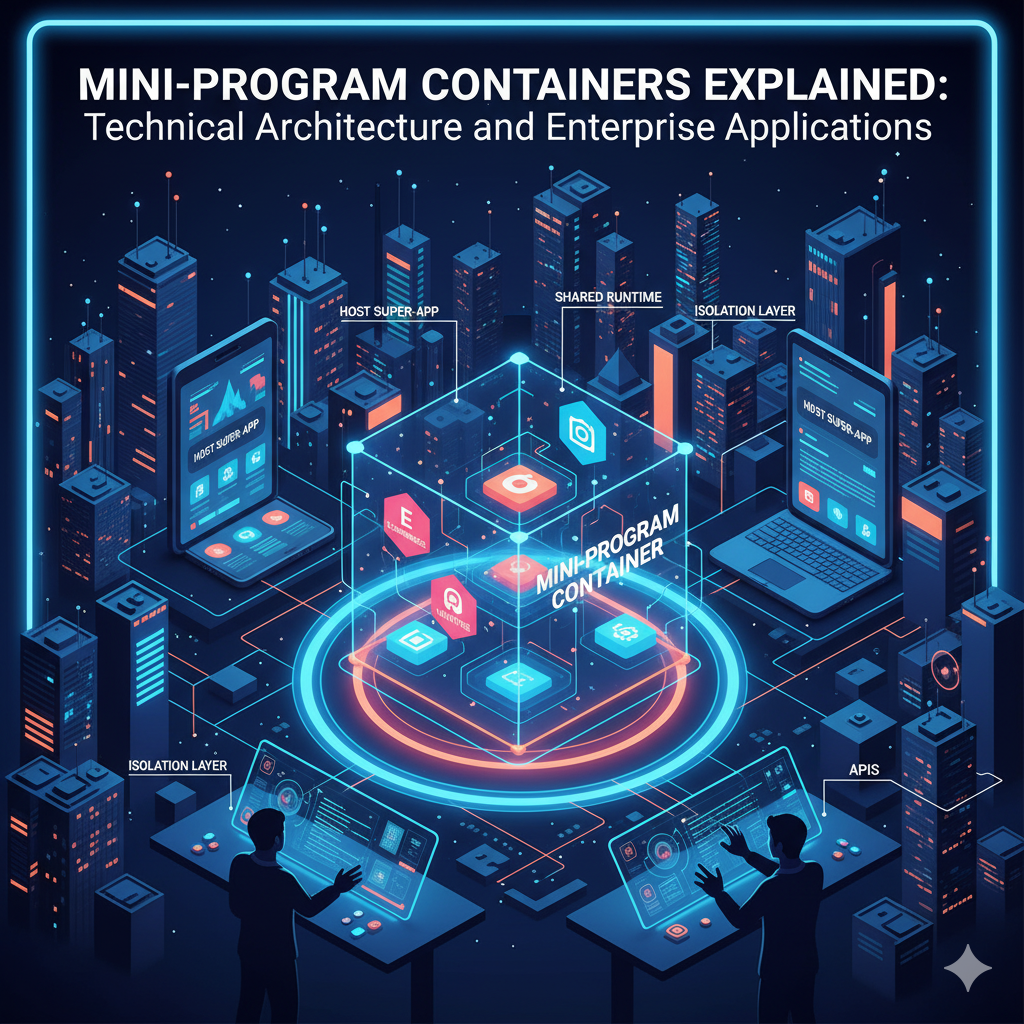
Mini-program containers represent a specialized class of runtime environments designed specifically for lightweight, isolated application components operating within larger host platforms. Unlike traditional virtual machines or container technologies optimized for server deployment, mini-program containers address unique requirements including mobile resource constraints, user interface integration, and security isolation for untrusted code execution. These technical foundations enable new application patterns where functionality can be dynamically integrated, updated, and composed within unified user experiences while maintaining stringent security and performance standards. For organizations evaluating architectural approaches for digital innovation, understanding mini-program container technology provides essential insights into contemporary application development paradigms.
Technical Architecture of Mini-Program Containers
Mini-program container architecture centers around several interconnected subsystems that collectively enable secure, efficient execution of isolated application components. The execution engine provides the runtime environment where mini-program code operates, typically implementing a sandboxed JavaScript or WebAssembly environment with controlled access to device capabilities and platform services. This engine balances execution efficiency with security isolation, preventing mini-programs from accessing unauthorized resources while enabling sufficient performance for interactive applications.
Resource management subsystems handle allocation and isolation of computing resources including memory, storage, and network access. Unlike traditional containers that assume cooperative resource sharing, mini-program containers must defend against potentially malicious components attempting to exhaust resources or interfere with other applications. Technical implementations include quota systems that limit resource consumption, priority-based allocation that ensures critical functionality receives necessary resources, and monitoring mechanisms that detect and respond to abnormal usage patterns.
Security enforcement represents perhaps the most distinctive aspect of mini-program container architecture. Multiple security layers work together to create defense-in-depth protection. Process isolation prevents mini-programs from directly accessing each other's memory spaces. Capability-based access control restricts system API usage based on declared permissions and runtime authorization checks. Communication channels implement encryption and authentication to prevent eavesdropping or tampering. These measures combine to create execution environments where untrusted code can operate safely within trusted platforms.
Integration Patterns with Host Platforms
Mini-program containers implement specialized integration patterns that enable seamless user experiences while maintaining technical separation from host platforms. User interface integration allows mini-programs to render visual components within host application contexts, creating the illusion of unified interfaces despite executing in isolated environments. Technical approaches include view composition systems that combine rendered outputs, event routing mechanisms that forward user interactions, and styling coordination that maintains visual consistency across component boundaries.
Service access patterns enable mini-programs to leverage platform capabilities while maintaining security controls. Rather than providing direct system access, host platforms expose controlled service interfaces that implement authentication, authorization, and audit logging. Common service categories include data storage with access controls, network communication with domain restrictions, and device hardware access with user consent requirements. These patterns balance functionality needs with security requirements in multi-application environments.
Lifecycle coordination ensures mini-programs operate correctly within broader application contexts. Host platforms manage component initialization based on user navigation patterns, suspending inactive components to conserve resources while maintaining state for rapid reactivation. Technical implementations include state preservation mechanisms, resource preloading strategies, and graceful degradation approaches that maintain functionality when ideal conditions cannot be met. These coordination patterns enable complex application compositions while maintaining system stability.
Enterprise Application Scenarios
Financial services organizations represent prominent adopters of mini-program container technology due to stringent security and compliance requirements. Banking applications use containerized mini-programs to integrate specialized financial services—including loan calculators, investment tools, and insurance products—within unified banking interfaces while maintaining regulatory-mandated isolation between different financial products. Technical implementations include transaction logging, audit trail generation, and access control enforcement that meets financial industry standards.
Retail and e-commerce platforms leverage mini-program containers to create dynamic marketplace experiences. Rather than developing monolithic applications that must encompass all merchant functionality, platforms provide container environments where merchants can deploy specialized storefronts, product catalogs, and promotional tools. This approach enables rapid innovation at the merchant level while maintaining platform security and user experience consistency. Performance optimization techniques ensure containerized storefronts operate efficiently even during peak shopping periods.
Healthcare organizations implement mini-program containers to integrate specialized medical functionality within patient portal applications. Container isolation ensures sensitive health data remains protected while enabling patients to access diverse healthcare services through unified interfaces. Technical considerations include HIPAA compliance validation, data encryption requirements, and access audit trails that demonstrate regulatory compliance across integrated component boundaries.
Performance Optimization Techniques
Mini-program containers employ specialized optimization techniques to address mobile platform constraints while maintaining security isolation. Startup performance receives particular attention since users expect near-instantaneous responsiveness when accessing containerized functionality. Common optimization strategies include preloading mechanisms that initialize containers before user interaction, caching approaches that persist execution states across sessions, and resource prioritization that allocates computing resources based on usage patterns.
Memory management represents another critical optimization area. Unlike server containers that can assume abundant memory resources, mobile environments impose strict constraints. Mini-program containers implement sophisticated memory management including garbage collection tuning for interactive applications, memory pooling to reduce allocation overhead, and proactive memory reclamation to prevent resource exhaustion. These techniques balance execution flexibility with resource conservation in constrained environments.
Network performance optimization addresses the unique characteristics of mobile connectivity. Mini-program containers implement intelligent caching strategies that account for variable network conditions, prefetching mechanisms that anticipate data requirements, and compression techniques that reduce transmission overhead. Security considerations influence these optimizations—encryption and authentication must not unduly impact performance, requiring careful implementation of cryptographic operations and protocol optimizations.
Security Implementation Details
Capability-based security models form the foundation of mini-program container protection systems. Rather than relying solely on process isolation, these models enforce fine-grained access controls based on declared capabilities. Mini-programs must explicitly request access to specific resources through capability declarations that undergo runtime validation. Technical implementations include capability derivation systems that limit privilege propagation, revocation mechanisms that terminate unauthorized access, and audit logging that tracks capability usage across application boundaries.
Communication security ensures protected data exchange between mini-programs and host platforms. Unlike traditional inter-process communication that assumes cooperative participants, mini-program containers must defend against malicious components attempting to eavesdrop or tamper with communications. Technical approaches include authenticated encryption for all communication channels, message integrity verification to detect tampering attempts, and forward secrecy mechanisms that protect past communications even if current encryption keys are compromised.
Runtime monitoring provides continuous security validation during mini-program execution. Unlike static analysis that examines code before execution, runtime monitoring observes actual behavior to detect security violations. Implementation techniques include system call interception to validate resource access, memory access monitoring to detect buffer overflow attempts, and control flow integrity verification to prevent code injection attacks. These monitoring systems operate with minimal performance impact while providing comprehensive security coverage.
Implementation Considerations for Enterprise Organizations
Platform selection involves evaluating multiple dimensions beyond basic functionality. Enterprises should assess container technology against specific requirements including integration capabilities with existing systems, compliance with industry regulations, and support for anticipated use cases. Technical evaluation should consider not only current needs but also anticipated future requirements as digital initiatives evolve. Business considerations include vendor stability, support quality, and ecosystem partnerships that influence long-term platform viability.
Development team preparation requires attention to both technical skills and architectural understanding. Unlike traditional application development where teams focus primarily on business logic implementation, mini-program container development involves distributed systems concepts, security isolation principles, and platform integration patterns. Effective preparation includes targeted training programs, hands-on experimentation with container technologies, and establishment of collaborative practices that support distributed component development.
Deployment strategy should balance innovation velocity with operational stability. Unlike monolithic applications where deployment represents a single coordinated event, mini-program container environments enable incremental component updates with varying risk profiles. Strategic approaches include phased rollout patterns that limit exposure during initial deployment, automated validation frameworks that verify component compatibility, and rollback mechanisms that enable rapid recovery when issues emerge. These patterns support sustainable innovation while maintaining system reliability.
Organizations implementing mini-program platforms should evaluate solutions that address both technical requirements and business objectives. Platforms like FinClip provide specialized container technology optimized for enterprise environments, offering capabilities including secure execution isolation, cross-platform compatibility, and integration with existing enterprise systems. This approach enables organizations to leverage mature platform technology rather than developing custom container implementations, accelerating digital innovation while maintaining security and compliance standards.
Read the FinClip developer docs to get started. View docs