App-in-App Architecture: Technical Foundations and Implementation Strategies

App-in-app architectures represent a fundamental shift in how applications are constructed, deployed, and experienced by users. Unlike traditional monolithic applications or loosely connected microservices, app-in-app approaches enable multiple independent mini-applications to operate within a single host container, creating cohesive user experiences while maintaining technical separation between components. This architectural pattern addresses persistent challenges in application evolution, team coordination, and user interface consistency while enabling new possibilities for functionality integration and ecosystem development. For organizations navigating digital transformation initiatives, understanding app-in-app fundamentals provides essential context for architectural decisions that balance immediate requirements with long-term strategic objectives.
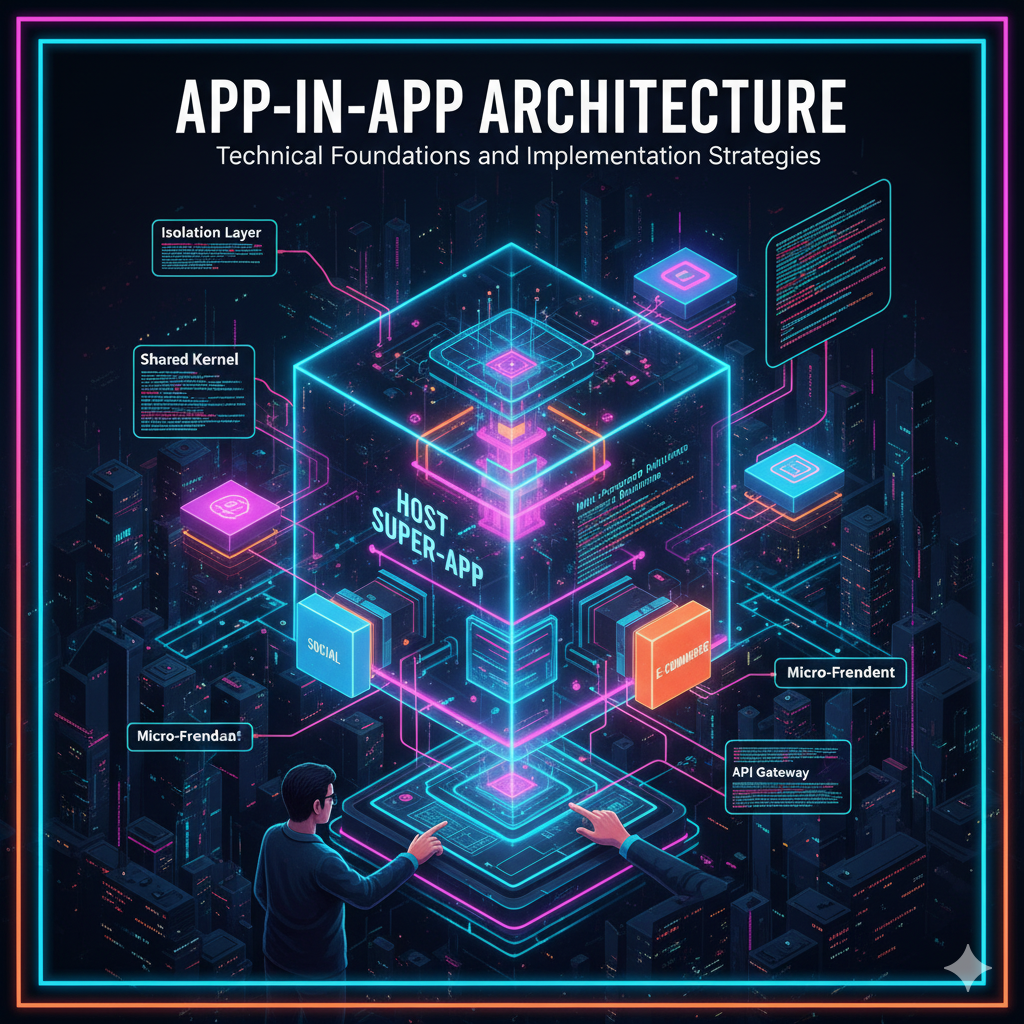
Technical Foundations of App-in-App Architectures
App-in-app architectures rely on several interconnected technical concepts that distinguish them from alternative approaches. At the core is the host container—a runtime environment that provides shared services while enforcing security boundaries between integrated mini-applications. This container typically implements sandboxing mechanisms that prevent mini-apps from accessing unauthorized resources or interfering with each other's operations. The technical implementation varies across platforms but generally includes process isolation, memory protection, and controlled inter-process communication channels.
Communication protocols represent another critical component. Mini-applications within app-in-app architectures require standardized methods for data exchange and event notification while maintaining security boundaries. Common approaches include message passing through controlled channels, shared memory with access controls, and remote procedure calls with authentication requirements. The specific protocol selection involves trade-offs between performance, security, and development complexity that must align with application requirements and platform capabilities.
Lifecycle management introduces additional technical considerations. Unlike traditional applications with single startup and shutdown sequences, app-in-app environments must coordinate multiple independent lifecycles. The host container typically provides lifecycle hooks that enable mini-apps to initialize resources, respond to foreground/background transitions, and cleanly terminate operations. Effective implementation requires careful attention to dependency management, resource cleanup, and error recovery to prevent issues in one mini-app from destabilizing the entire environment.
Implementation Patterns and Best Practices
Successful app-in-app implementations follow several established patterns that address common challenges while optimizing developer productivity and system reliability. The plugin architecture pattern enables mini-apps to register capabilities with the host container, which then coordinates their execution based on user interactions and system events. This approach provides substantial flexibility while maintaining clear separation of concerns between the host environment and integrated components.
Version management represents another critical implementation consideration. Mini-applications within app-in-app architectures typically evolve independently, creating potential compatibility issues when components expect different interfaces or data formats. Effective version management strategies include backward compatibility requirements, version negotiation protocols, and graceful degradation mechanisms that maintain functionality when perfect compatibility cannot be achieved. These approaches enable incremental innovation while preserving system stability as components evolve.
Performance optimization requires specialized techniques in app-in-app environments. Resource sharing between mini-apps can create contention that affects user experience if not properly managed. Common optimization strategies include lazy loading of infrequently used components, intelligent caching of shared resources, and prioritized resource allocation based on user interaction patterns. Implementation teams must balance optimization efforts against development complexity to achieve sustainable performance improvements.
Organizational Implications and Team Coordination
App-in-app architectures fundamentally change how development teams organize and collaborate. Unlike monolithic applications requiring tight coordination across all components, app-in-app approaches enable distributed development where teams own specific mini-applications with clearly defined interfaces and dependencies. This organizational model supports several beneficial patterns including specialized expertise development, independent release cycles, and focused quality assurance efforts.
Coordination mechanisms must adapt to support this distributed development approach. Interface definition becomes a critical coordination point, with clear specifications and version management protocols enabling teams to evolve their components independently while maintaining system integrity. Integration testing frameworks provide automated validation that components continue operating correctly as they evolve, reducing coordination overhead while maintaining quality standards.
Cultural considerations also influence successful implementation. Teams accustomed to tight coupling in monolithic applications may initially struggle with the autonomy and responsibility inherent in app-in-app approaches. Effective leadership addresses these challenges through clear communication of architectural benefits, establishment of collaborative norms around interface management, and recognition of team contributions to the broader system's success. The resulting cultural alignment supports sustainable implementation of distributed architectural patterns.
Security and Compliance Considerations
Security implementation in app-in-app environments requires specialized approaches that address unique threat vectors. Sandboxing mechanisms must prevent not only external attacks but also lateral movement between integrated mini-applications. Implementation typically involves multiple security layers including process isolation, capability-based access control, and encrypted inter-process communication. These measures combine to create defense-in-depth architectures that maintain security even when individual components contain vulnerabilities.
Data protection introduces additional complexity in multi-application environments. Mini-applications often require access to shared data while maintaining appropriate isolation based on sensitivity levels and regulatory requirements. Technical approaches include data partitioning with access controls, encrypted data sharing with key management protocols, and audit logging that tracks data access across component boundaries. Compliance validation must consider both individual component behaviors and their interactions within the integrated environment.
Regulatory compliance often drives specific architectural decisions. Industries including finance, healthcare, and government services face stringent requirements regarding data handling, audit trails, and access controls. App-in-app implementations must demonstrate compliance not only for the host container but also for all integrated mini-applications and their interactions. This comprehensive approach requires coordination between technical implementation teams and compliance specialists throughout the development lifecycle.
Getting Started with App-in-App Implementation
Organizations exploring app-in-app architectures should begin with careful assessment of their specific requirements and constraints. Technical evaluation should consider existing infrastructure, team capabilities, and performance expectations while identifying potential integration challenges. Business analysis should align architectural decisions with strategic objectives including time-to-market requirements, scalability needs, and ecosystem development goals. The resulting assessment informs implementation planning that balances technical feasibility with business value.
Platform selection represents a critical early decision. Organizations must evaluate available container technologies based on several dimensions including security capabilities, development tooling, performance characteristics, and ecosystem support. For enterprises implementing mini-program architectures, solutions like FinClip provide specialized app-in-app capabilities that integrate with existing enterprise environments while maintaining security standards and development flexibility. This approach enables organizations to leverage established platforms rather than developing custom container implementations.
Implementation should follow iterative patterns that enable learning and adaptation. Initial phases should focus on core functionality with clear success metrics, allowing teams to validate architectural decisions before committing substantial resources to full-scale implementation. As experience accumulates, organizations can expand implementation scope while incorporating lessons learned from earlier phases. This adaptive approach supports sustainable architecture evolution aligned with organizational capabilities and market requirements.
App-in-app architectures provide substantial advantages for enterprises implementing digital transformation initiatives in regulated environments. Solutions like FinClip enable organizations to deploy specialized mini-program platforms with device-side security isolation, supporting complex application ecosystems while maintaining compliance with industry standards. This approach demonstrates how modern architectural patterns can address both technical requirements and business objectives in enterprise computing environments.
Explore FinClip ChatKit—open-source AI chat middleware. GitHub